From Singapore-based Exchange DragonEx Monday officially announced on March 24 said it suffered a hacker attack, some users of the exchange and crypto funds “were transferred and theft.” According to preliminary statistics from PeckShield, the DragonEx exchange lost a total of $6,028,283 worth of digital assets, and digital assets worth $929,162 have flowed into the exchange. Currently, there is still $5,099,121 worth of digital assets in the hands of hackers.
When DragonEx first discovered an attack on Sunday, it first took its platform offline and said it was upgrading its system. Later that same day, it was said to be “still in system maintenance.”
DragonEx said in a notice on Monday that “some assets will be recovered and we will try our best to recover the remaining stolen assets.” The exchange further stated that it has notified the various judicial agencies, including Estonia, Thailand, Singapore, and Hong Kong, of the hacking incident and added:
[ads-quote-center cite=”]”We are assisting the police in conducting investigations. All platform services will be closed and accurate asset loss recovery will be announced within a week. DragonEx will be liable for any loss to users.” [/ads-quote-center]
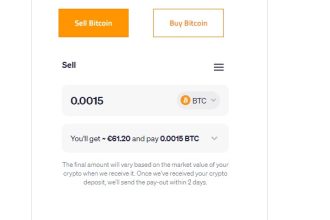
DragonEx has released a wallet address for 20 cryptocurrencies, claiming that stolen funds have been transferred to these addresses. The list includes the top five cryptocurrency addresses of market capitalization: Bitcoin (BTC), Ethereum (ETH), XRP, Litecoin (LTC) and EOS, in addition to the address of six Tether stable USDT.
DragonEx said, “We sincerely request the help of all our peers and other industry forces, please help us investigate the whereabouts of assets, freeze and stop the flow of assets.” It also said that the hackers transferred to the Huobi and gate.io exchanges stolen encryption The asset has been blocked.
According to a preliminary analysis by PeckShield’s security personnel, the hacker’s high probability is to implement digital asset batch transfer by stealing the exchange wallet private key or illegally accessing the API server.