AI Cybersecurity Tools Every Small Business Owner Needs — With advanced technology transforming the digital landscape of small business protection, some cybersecurity solutions are nothing short of a miracle.
- Key Poinst & AI Cybersecurity Tools Every Small Business Owner Needs Now
- 10 AI Cybersecurity Tools Every Small Business Owner Needs Now
- 1. Darktrace
- 2. CrowdStrike Falcon
- 3. IBM Watson
- 4. CylancePROTECT
- 5. Splunk Enterprise
- 6. Vectra AI
- 7. Rapid7 InsightIDR
- 8. FireEye Helix
- 9. SentinelOne
- 10. Palo Alto Networks Cortex XDR
- How We Choose AI Cybersecurity Tools Every Small Business Owner Needs Now
- Conclusion
- FAQ
You will explore the role of AI powered tools in threat detection, prevention of cyber attacks, and securing sensitive data instantaneously.
The guide will also point important solutions towards today’s digital space which makes safety, efficiency and overall cybersecurity readiness better.
Key Poinst & AI Cybersecurity Tools Every Small Business Owner Needs Now
Darktrace uses AI to detect unusual network behavior and stop threats before damage occurs.
CrowdStrike Falcon provides real-time endpoint protection using AI to identify and neutralize cyber threats quickly.
IBM Watson for Cyber Security analyzes massive data to identify threats, helping businesses respond faster to cyber incidents.
CylancePROTECT prevents malware using AI instead of traditional signature-based detection, improving proactive security significantly.
Splunk Enterprise Security uses AI to monitor systems, detect anomalies, and provide actionable cybersecurity insights instantly.
Vectra AI detects hidden cyberattacks in real time by analyzing network traffic using artificial intelligence.
Rapid7 InsightIDR combines AI with behavior analytics to detect suspicious activities across users and systems.
FireEye Helix integrates AI-driven analytics to identify threats and automate responses across security environments effectively.
SentinelOne uses AI to autonomously detect, prevent, and respond to cyber threats across devices.
Palo Alto Networks Cortex XDR leverages AI to correlate data and detect sophisticated cyberattacks across systems.
10 AI Cybersecurity Tools Every Small Business Owner Needs Now
1. Darktrace
Darktrace is an AI-based cybersecurity application that learns what normal behavior looks like within your business network.
It continuously observes systems, users, and devices for unusual activity in real time. For small business owners, this means you can detect threats for example ransomware, phishing attempts or insider attacks sooner without a large IT department.
Its autonomous response feature can quietly respond instantly to snuff out threats before they spread. Darktrace learns to fit in your specific environment and mitigate the threat of an attack, being quite a literally powerful business practice towards you maintaining a progressive form of cybersecurity
| Feature | Explanation |
|---|---|
| Self-Learning AI | Learns normal network behavior and detects deviations automatically without manual configuration or constant human monitoring. |
| Real-Time Threat Detection | Continuously monitors systems and instantly identifies unusual activities like ransomware, phishing, or insider threats. |
| Autonomous Response | Takes immediate action to contain threats, minimizing damage without waiting for human intervention or approval. |
| Adaptive Security | Adjusts protection based on your business environment, ensuring personalized and evolving cybersecurity defense strategies. |
2. CrowdStrike Falcon
Product DescriptionCrowdStrike Falcon is an Artificial Intelligence (AI) that can work as a cloud-based endpoint security platform to protect organization devices- laptops, desktops, and servers.
It provides real-time threat detection, prevention and response capabilities which help small businesses with limited cybersecurity resources.
Endpoint Falcon virtually collects data and analyze it detecting any suspicious behavior, promptly stopping attacks.
Its lightweight approach ensures it leaves almost no footprint on the system while still providing solid protection.
Besides, it offers detailed insights and report encouraging the business owners about all possible risks. CrowdStrike Falcon is designed to scale; as your business grows and evolves, its architecture will scale with you for years of security.
| Feature | Explanation |
|---|---|
| Cloud-Based Protection | Delivers security through cloud infrastructure, reducing hardware requirements and simplifying deployment for small businesses. |
| Real-Time Threat Detection | Identifies and blocks threats instantly using AI-driven behavioral analysis across all connected devices. |
| Lightweight Agent | Runs efficiently on devices without slowing performance, ensuring smooth business operations alongside strong security. |
| Scalable Architecture | Easily grows with your business, supporting more devices and users without compromising protection quality. |
3. IBM Watson
IBM Watson for Cyber Security uses AI deep learning and machine learning to sift through the massive amount of structured and unstructured cyber security data.
By correlating information from security logs and global threat intelligence, it helps small businesses detect threats faster.
By integrating with Watson which was able to analyze natural language, it was possible for the Watson system to read through security research and reports and find hidden threats.
This cuts down the time needed for threat detection and fast-tracks decision making. It serves as a virtual security analyst for small business owners, providing actionable insights coupled with recommendations.
And it has relentless learning capabilities that let your defenses remain in pace with new cybersecurity challenges.
| Feature | Explanation |
|---|---|
| AI Data Analysis | Processes large volumes of structured and unstructured data to identify hidden cybersecurity threats quickly. |
| Natural Language Processing | Understands and analyzes security reports and research to uncover insights from human language data. |
| Threat Correlation | Combines multiple data sources to detect complex threats that may go unnoticed individually. |
| Continuous Learning | Improves over time by learning from new data, ensuring up-to-date protection against evolving cyber risks. |
4. CylancePROTECT
CylancePROTECT is an advanced form of antivirus solution that uses AI to stop cyber attacks before they execute.
CylancePROTECT detects and blocks malware in a proactive fashion using predictive models rather than relying on signature based updates like traditional antivirus tools.
This makes it very powerful in response to new and unknown threats. This is light enough to require fewer system resources and maintenance, which is great for small businesses.
It also works offline, which increases protection when users are not connected to the Internet, as is increasingly happening.
Simplicity is the theme for businesses seeking modern protection without requiring constant updates or manual intervention, and that makes CylancePROTECT a breeze to implement.
Built on machine-learning technology to eliminate what it calls “the costly overhead of frequent updates,” enterprises find that instantaneous response disruptive to threat development results in “”an enterprise-level antivirus product” without the inefficiencies normally found in ever-present security systems.
| Feature | Explanation |
|---|---|
| Predictive Threat Prevention | Uses AI models to block malware before execution instead of relying on traditional signature detection. |
| Offline Protection | Provides strong security even without internet connectivity, ensuring continuous protection in all environments. |
| Lightweight Performance | Consumes minimal system resources, allowing devices to run smoothly without performance degradation. |
| Zero-Day Protection | Detects and blocks previously unknown threats, protecting against emerging and sophisticated cyberattacks. |
5. Splunk Enterprise
This is Splunk Enterprise Security, a mature security information and event management (SIEM) platform that leverages AI/ML to continuously monitor and correlate all data across your IT environment.
It gathers logs from multiple systems and detects anomalies that may represent cyber threats. It gives small businesses one place to see security events, helping them quickly detect and respond to any incidents that take place.
The platform’s automation means little manual work, allowing small teams to keep on top of cyber security while still hitting back hard against rapidly evolving threats.
| Feature | Explanation |
|---|---|
| Centralized Monitoring | Collects and analyzes logs from multiple systems, providing a unified view of security events. |
| Advanced Analytics | Uses AI and machine learning to detect anomalies and identify potential cyber threats quickly. |
| Custom Dashboards | Offers flexible dashboards for visualizing security data, making insights easy to understand and act upon. |
| Automation Capabilities | Automates repetitive security tasks, reducing manual workload and improving response efficiency. |
6. Vectra AI
Vectra AI, for example, specializes in network detection and response by leveraging artificial intelligence to analyze traffic and expose stealthy threats.
It can identify such attacker behaviors as lateral movement, credential theft and command-and-control communication in real-time.
Vectra AI offers small business owners the level of visibility into network activity they typically need without requiring overly complicated setups.
Because it is powered by AI, the false positives are extremely low and usually only authentic threats will be detected.
Allowing enterprizes & businesses to get used to this quickly and efficiently. This capability continuously learns network patterns, and Vectra AI fortifies your defenses against sophisticated attacks that evade conventional security tools.
| Feature | Explanation |
|---|---|
| Network Traffic Analysis | Monitors and analyzes network traffic to detect suspicious patterns and malicious activities. |
| Behavior-Based Detection | Identifies attacker behaviors like lateral movement and credential theft using AI models. |
| Reduced False Positives | Focuses on real threats, minimizing unnecessary alerts and improving response efficiency. |
| Real-Time Visibility | Provides continuous insights into network activities, helping businesses detect threats instantly. |
7. Rapid7 InsightIDR
Rapid7 InsightIDR is a cloud-based detection and response solution which uses AI, user behaviour analytics, and EndPoint monitoring.
This helps small businesses to spot unusual behaviour such as a hacked account, insider threat or person trying to access accounts they are not supposed to get into.
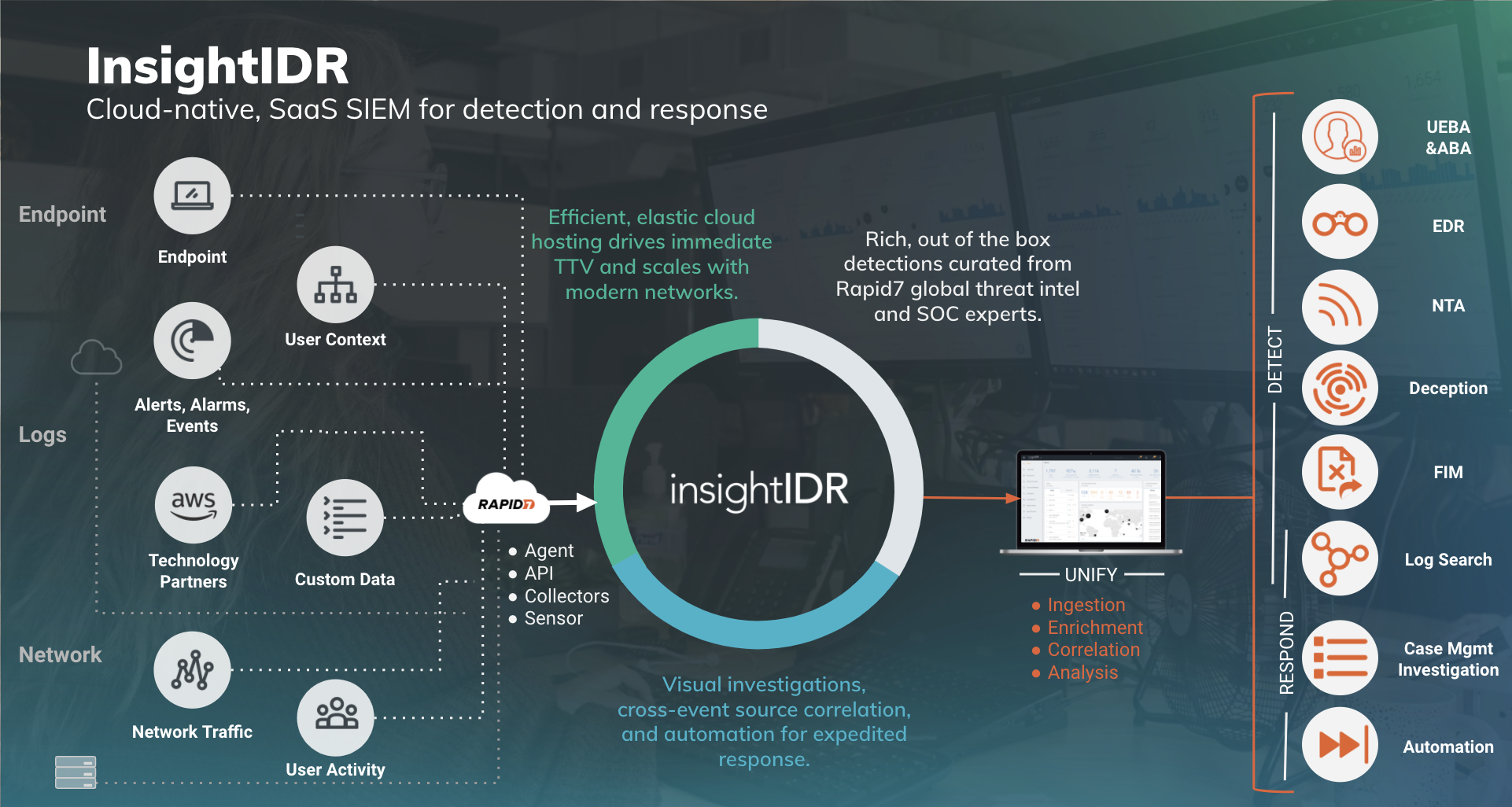
With real-time alerts and fully automated investigations, InsightIDR cuts the time it takes to respond to incidents. It has a user friendly interface that allows for both experts and non-experts use security events.
It provides a complete perspective on your security posture by combining data across various sources. This is what makes Rapid7 InsightIDR an actionable, potent solution for augmenting cyber security in a non-resource-exhaustive manner.
| Feature | Explanation |
|---|---|
| User Behavior Analytics | Tracks user activities to identify suspicious actions and potential insider threats effectively. |
| Real-Time Alerts | Sends instant notifications when unusual activities or potential breaches are detected. |
| Automated Investigations | Automatically analyzes incidents, reducing response time and simplifying threat management processes. |
| Cloud-Based Platform | Offers easy deployment and scalability without requiring complex on-premise infrastructure setups. |
8. FireEye Helix
FireEye Helix is AI-driven analytics security operations platform for threat detection, investigation and response.
It combines data from numerous security tools into a single place, allowing you to have an overview of your organization’s security field.
Helix automates threat detection and response processes, reducing complexity for security operations within small businesses.

The product also taps global threat intelligence to detect new threats. This ensures that your organization is protected against novel cyberattacks.
FireEye Helix offers a scalable architecture that can help smaller businesses achieve enterprise-level security, without needing an army of technicians.
| Feature | Explanation |
|---|---|
| Unified Security View | Integrates data from multiple tools to provide a centralized view of security operations. |
| AI-Driven Analytics | Uses artificial intelligence to detect, investigate, and respond to threats efficiently. |
| Threat Intelligence Integration | Leverages global threat intelligence to identify emerging cyber risks proactively. |
| Automated Response | Streamlines security workflows by automating detection and response actions across environments. |
9. SentinelOne
SentinelOne: SentinelOne is an AI-enabled endpoint security solution that automatically protects against cyber threats.
It is capable of detecting, preventing and responding to attacks automatically without the need for human intervention.
This means good security — little work required to do so on the part of small business owners. SentinelOne utilizes behavioral AI to detect signs of nefarious actions and can automatically restore devices to safety post-attack.
It boasts a centralized management console that delivers complete visibility into every endpoint. Easy Monitoring and Control of Security Across Devices SentinelOne takes care of this automatically, so it is always on and working as intended in the background.
| Feature | Explanation |
|---|---|
| Autonomous Protection | Detects and responds to threats automatically without requiring human intervention. |
| Behavioral AI Detection | Identifies malicious behavior instead of relying on known threat signatures. |
| System Rollback | Restores systems to a safe state after an attack, minimizing data loss and downtime. |
| Centralized Management | Provides a single dashboard to monitor and manage all endpoints efficiently. |
10. Palo Alto Networks Cortex XDR
Cortex XDR is an extensible, endpoint-based detection and response product developed by Palo Alto Networks that employs artificial intelligence to mine from data in the endpoint, network and the cloud.
Cross-references information on these sources to detect intricate cyber threats that would otherwise remain undetected.
From point product integration to threat detection and response, Cortex XDR is a powerful security platform for small businesses.
It even has automated workflows that help reduce manual processes, making it more efficient and saves time.
Providing complete visibility and proactive defense, it enables businesses to remain one step ahead of evolving threats and secure a strong cyber-defense posture in an increasingly digital world.
| Feature | Explanation |
|---|---|
| Cross-Data Correlation | Combines data from endpoints, networks, and cloud to detect advanced threats effectively. |
| Extended Detection & Response | Provides comprehensive visibility and response capabilities across multiple environments. |
| Automated Workflows | Reduces manual effort by automating threat detection, investigation, and response processes. |
| Proactive Threat Hunting | Uses AI to identify hidden threats early, improving overall cybersecurity posture. |
How We Choose AI Cybersecurity Tools Every Small Business Owner Needs Now
Understand Your Needs Select any tool only after identifying critical data, systems and main risks. (TechTarget)
Focus on Essential Protection Prioritize the tools for endpoints, email security, backups and network protection. (ITU Online IT Training)
Check AI Capabilities Via the AI for real-time threat detection and automated response in the tool.
Ease of Use Choose simple tools that you can effectively manage even without a full IT team.
Scalability Choose tools that are able to evolve with your business as you grow.
Budget-Friendly Options To some extent, try not to pay too much for features of tools that you will not fully use.
Integration Support It can integrate well with your other programs and systems.
Real-Time Monitoring Choose tools which provide constant monitoring and immediate alerts
Vendor Reputation & Support Choose reputable vendors with positive reviews, support and relevant experience. (TechTarget)
Conclusion
ConclusionAI Cybersecurity Tools for Small Business Owners Every Owner Must Have Now To Secure Digital Assets
Catch Threats Early And Prevent Costly Cyber Attacks With features such as real-time monitoring, automation and intelligent threat analysis these solutions are rendering exemplary service.
The right AI tools allow small businesses to improve security, mitigate risks, and remain ahead of the continuously changing cyber landscape in this modern digital world.
FAQ
What are AI cybersecurity tools?
AI cybersecurity tools are software solutions that use artificial intelligence to detect, prevent, and respond to cyber threats automatically in real time.
Why do small businesses need AI cybersecurity tools?
Small businesses need them because they face increasing cyberattacks but often lack large IT security teams or advanced protection systems.
How do AI cybersecurity tools work?
They analyze network behavior, detect unusual activity, and automatically respond to threats using machine learning algorithms.
What types of threats do these tools detect?
They detect malware, ransomware, phishing attacks, unauthorized access, and unusual network behavior.











